When to Implement a Content Publishing Approval Process
Implementing a content publishing approval process is vital for ensuring quality, especially with multiple contributors or sensitive content. It can maintain brand reputation, enforce legal[…]
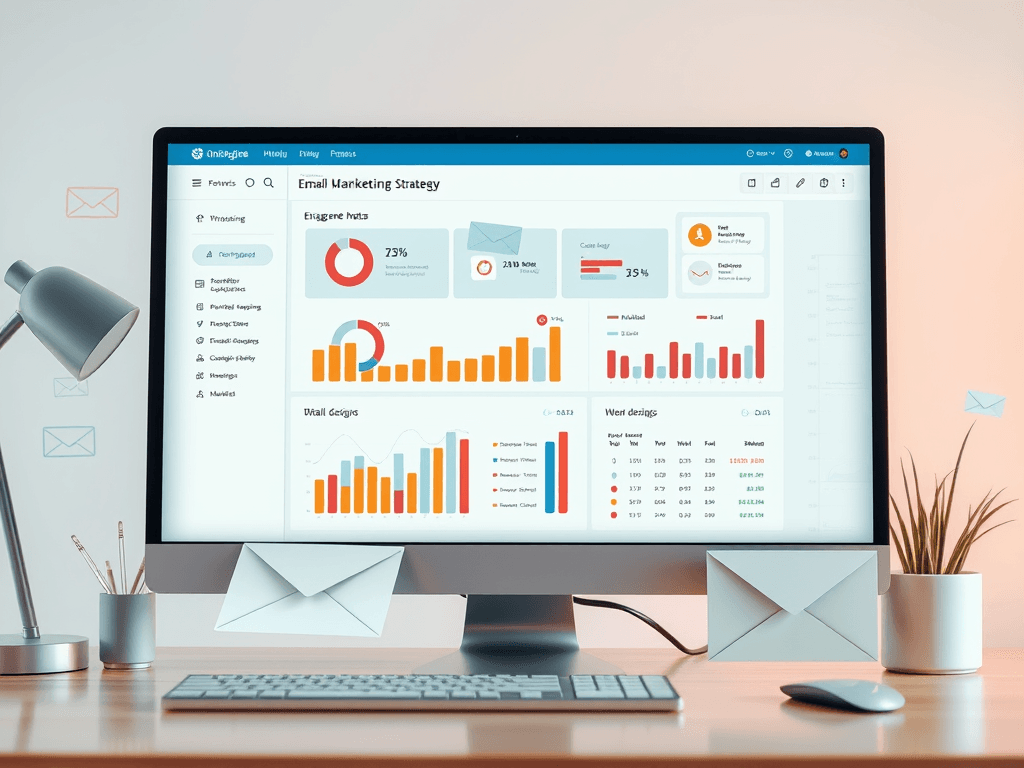
Mastering Email Marketing: Strategies to Promote Yourself Effectively
Understanding Email Marketing Email marketing is a powerful tool for self-promotion. It allows you to connect directly with your audience, share valuable information, and establish[…]
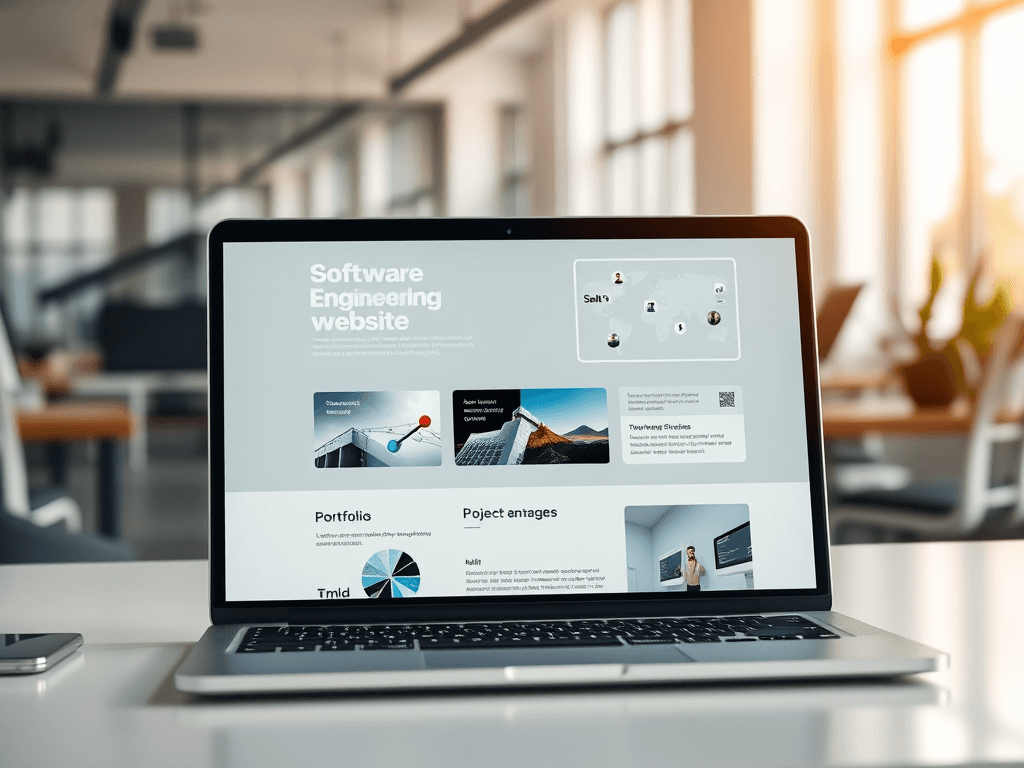
Optimize Your Software Engineering Website for Success
Creating a powerful website for a software engineering business involves more than showcasing coding skills; it must communicate value to non-technical clients. A well-structured site[…]
Exploring the Diverse Applications of Multimedia in Today’s World
Multimedia integrates text, audio, images, animations, and video to enhance engagement across several domains, including education, marketing, entertainment, and business communication. It promotes interactive learning,[…]

Why Choose Archer IT Solutions for Your Technical Support Needs?
Archer IT Solutions excels in IT support and web hosting, offering expertise, comprehensive services, and competitive pricing. With rapid response times under 24 hours, they[…]

Enhancing WordPress Functionality with Effective Support
Understanding the Importance of IT Support for WordPress Hosting Managing a WordPress site comes with many responsibilities, and effective support is crucial for seamless operation.[…]

Effective Link-Building Strategies for SEO Success
Building a Strong Link-Building Strategy for Your Website Creating a solid link-building strategy is crucial for improving your site’s SEO and driving traffic. Here are[…]

Top Benefits of SSL for Your Website Security
Why You Should Use SSL for Your Website Implementing SSL (Secure Socket Layer) on your website is crucial for ensuring the security and integrity of[…]

Understanding Firewalls: Safeguarding Your Network Effectively
A firewall serves as a security system that monitors and controls network traffic based on established rules, protecting against unauthorized access and cyber threats. It[…]